| view 👀:267 |
🙍 oneddl |
redaktor: wertyozka | Rating👍:
Cybrary - Penetration Testing and Ethical Hacking
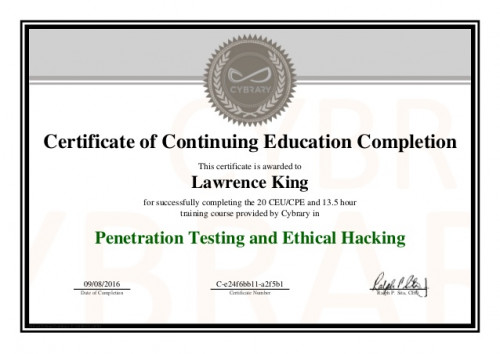
Cybrary - Penetration Testing and Ethical Hacking
English | Size: 2.42 GB
Category: Tutorial
this is one of the famous courses of cybrary for ethical hacking.
Module 01 - Phases of Penetration Testing
1º Passive or Active Information Gathering or Reconnaissance2º Scanning the target3º Gaining access to the system or server4º Maitaining Access5º Covering the tracks
Module 10 - Denial of Service
DDoS, rDDoS, DoS, rDoS1. ConceptsReducesRestrictsPreventsFloods2. ImpactsLoss of goodwillDisable NetworksDisable organizationFinancial loss3. DetectionActive profile analysisChange point analysis4. TechniquesBandwidth FloodSYN Flood (3 Way-Handshake)
Module 11 - Session Hijacking
It's a Kali Linux and Windows tool for session hijacking
Module 12 - Hacking Web Servers
Hacking WebServers1. ProductsIIS 17%Apache 65%Nginx 13%GoogleLightHTTPD2. ImpactWeb defacementCompromisesData tampering" " TheftPivot Points (To get inside the internal network)3. TechniquesDirectory traversalHTTP Response splittingWeb cache poisonSS
Module 13 - Web Applications
Another HTTP tool to query web servers for indentification.
Module 14 - SQL Injection
SQL Injection (CheatSheet)1. ConceptsHTTP Post RequestNormal code analysisUpdateSelect, WhereFrom "mytable"Drop2. AttacksRemote code executionAvailabilityBypass auth admin' --Info disclosureData integrityPassword grabbingXFER whole DBOS interaction3.
Module 15 - Wireless
Wireless Hacking1. ConceptsExtension to wiredMulti Access Points3G/4G HotspotsLAN to LAN2. Standards802.11 A / B (2.4GHz)/ G (2.4GHz)/ I (WPA2)/ N / 16 (WIMAX)3. ComponentsSSID (Wireless Name)OpenShared KeyAuth ComponentsBSSID (MAC)4. AntennasDirecti [view]
Module 16 - Mobile Hacking
Mobile Hacking1. TerminologyROMBrickingBYOD (Bring Your Own Device)2. VulnerabilitiesApp storesMobile malwareApp sandboxingEncryptionJailbreaking / RootingPrivacy / GeolocationPhysical3. PlatformsAndroidMac OSBlackberryWindows4. AttacksMalware -->
Module 17 - IDS, Firewalls & Honeypots
Evading IDS / IPS, Firewalls and Honeypots1. ConceptsPlacementHIDS - HIPSNIDS - NIPSPort ScanFirewalling2. CategoriesIntegrityProfileAnomaly (Protocl)StatisticalSignatureKnowledge (Rule)Behavior3. FW ArchitecturesBastion hostScreened subnetMulti home
Module 18 - Buffer Overflows
StackExecuting it via GDB(gdb) set disassembly-flavor intel(gdb) listNormal execution of the code(gdb) run $(perl -e 'print "A"x10;')Starting program: /root/Desktop/Notes on Certifications/CEH/stack $(perl -e 'print "A"x10;')The value is AAAAAAAAA
Module 19 - Cryptography
Download the advanced encryption package for windows to test it.
Module 02 - Footprinting
Lauch application and choose your target... 3:)We will have a report...We can make reportsView synopsisCreate chartsGet GeoLocationLog ViewerStats
Module 03 - Scanning
ON the OSI Model we will use IPv4 - IPv6 - ICMPTCP(Flags) UDPBasics- Hosts { UP/Down- Ports/Services { Available/Responding- Vulnerabilities { On the target- Diagrams (no need to scan) Technics- Ping Sweep- Subnet Masks- TCP (SRAF UP - SYN; RST; ACK
Module 04 - Enumeration
Windows PSTools are located in:c:\> dir \windows\system32\ps*c:\> dir \windows\system32\ps*.exe
Module 05 - System Hacking
Snow is a steganography toolWill be used to hide information on files.snow -C -m "This is the hidden message that cannot be found" -p "password" snow.txt snowsteg.txtExtract the informationsnow -C -p "password" snowsteg.txt
Hope it helps. thank you.
Buy Long-term Premium Accounts To Support Me & Max Speed
DOWNLOAD:
DOWNLOAD:

https://rapidgator.net/file/09eb02bbf2d9b101208d7765ba5abfc5/[Cybrary]_Penetration_Testing_and_Ethical_Hacking.part1.rar.html
https://rapidgator.net/file/60803f09551864586ca0e97cbd39eab3/[Cybrary]_Penetration_Testing_and_Ethical_Hacking.part2.rar.html
https://rapidgator.net/file/64cdf799e27f510010583517a3e8857b/[Cybrary]_Penetration_Testing_and_Ethical_Hacking.part3.rar.html
https://rapidgator.net/file/3e01d0e7bf9eb329eed86a0d94fccb34/[Cybrary]_Penetration_Testing_and_Ethical_Hacking.part4.rar.html

If any links die or problem unrar, send request to https://goo.gl/aUHSZc
⚠️ Dead Link ?
You may submit a re-upload request using the search feature.
All requests are reviewed in accordance with our Content Policy.
Comments (0)
Users of Guests are not allowed to comment this publication.